Question: Why do ERP systems fail? Perform an
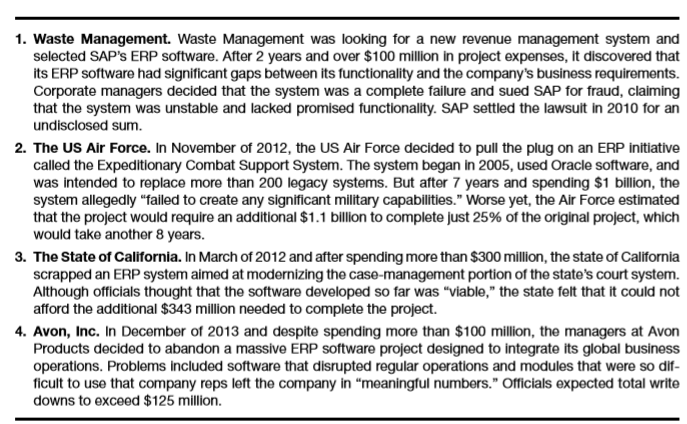
Why do ERP systems fail? Perform an Internet search on this topic and identify a new ERP failure not listed in Figure 5-8. Prepare a one page report describing the failure and providing reasons why it happened. Be sure to include information about the costs or inconveniences caused by the failure.
Figure 5-8:
Transcribed Image Text:
1. Waste Management. Waste Management was looking for a new revenue management system and selected SAP's ERP software. After 2 years and over $100 million in project expenses, it discovered that its ERP software had significant gaps between its functionality and the company's business requirements. Corporate managers decided that the system was a complete failure and sued SAP for fraud, claiming that the system was unstable and lacked promised functionality. SAP settled the lawsult in 2010 for an undisclosed sum. 2. The US Air Force. In November of 2012, the US Air Force decided to pull the plug on an ERP initiative called the Expeditionary Combat Support System. The system began in 2005, used Oracle software, and was intended to replace more than 200 legacy systems. But after 7 years and spending $1 billion, the system allegedly "failed to create any significant military capabilities." Worse yet, the Air Force estimated that the project would require an additional $1.1 billion to complete just 25% of the original project, which would take another 8 years. 3. The State of California. In March of 2012 and after spending more than $300 million, the state of California scrapped an ERP system aimed at modernizing the case-management portion of the state's court system. Although officials thought that the software developed so far was “viable," the state felt that it could not afford the additional $343 million needed to complete the project. 4. Avon, Inc. In December of 2013 and despite spending more than $100 million, the managers at Avon Products decided to abandon a massive ERP software project designed to integrate its global business operations. Problems included software that disrupted regular operations and modules that were so dif- ficult to use that company reps left the company in "meaningful numbers." Officials expected total write downs to exceed $125 million.
> Do you understand PERT charts? Refer back to Figure 13-10 and answer the following questions: a. Which activity or activities must be completed before activity C can begin? b. Which activity or activities must be completed before activity G can begin? c.
> Identify a particular information system that is not working very well and perform a preliminary investigation of it. In your work, be sure to talk to (1) at least one external “customer” who is affected by the system, (2) one employee who uses the syste
> Are software developers cheap or expensive? That’s important because developing custom software for your accounting system depends in part on how much such labor will cost. To find out, access government statistics from the Bureau of Labor Statistic’s Occ
> Cook Consultants is currently in the process of completing the systems implementation activities for converting Samuel Company’s old system to a new one. Because of unexpected delays in performing specific implementation activities, Jerry Hazen, the proje
> Guess Right Consultants is a New Zealand business that helps clients with financial planning—especially preparing wills, creating trusts, and allocating funds among competing investment categories. It’s not an unusual business, but the company has not bee
> Jay Beck works for the AAZ Consulting Firm. His friend, Hank Henley, is the general manager and majority stockholder of the Pacific Worldwinds, a professional football team. Hank asked Jay to design an online, real time computer system for “the efficient o
> Even if you are now only a student with limited or no work experience, it is not too early to begin building a professional identity and your own company—Me, Inc. This is an identity that you’ll want to post and carefully cultivate on some of the popular
> Stevenson Apparel is a manufacturer of fashion apparel that has just opened its first large retail store for selling in-season clothes at regular prices. The company’s competitive strategy depends on a comprehensive point of-sale (POS) system supporting o
> The Chris Hall Company manufactures and distributes low-priced bottled wines to retailers. You are hired as a management consultant to help this company solve some of its systems problems. Describe the types of decision-making information that probably w
> Visit the website “How Flowcharts Help Companies Save Money, Get Accurate Audits, and Satisfy the Government” at: http://mapthink .blogspot.com/2012/10/how-flowcharts-help -companies-save.html. According to this site, how do flowcharts help save companies
> Follow the directions in Problem 12-11 to access Excel’s drawing tools, and then recreate the two program flowcharts shown in Figure 12-21. Draw each flowchart on a separate work sheet. Rename the ï&no
> The Bridget Joyce Company is an office products distributor that must decide what to do with delinquent credit-sales accounts. Mr. Bob Smith, the credit manager, divides accounts into the following categories: (1) accounts not past due, (2) accounts 30 da
> The Jeffrey Getelman Publishing Company maintains an online database of subscriber records, which it uses for preparing magazine labels, billing renewals, and so forth. New subscription orders and subscription renewals are keyed into a computer file from
> The LeVitre and Swezey Credit Union maintains separate bank accounts for each of its 20,000 customers. Three major files are the customer master file, the transaction file of deposits and withdrawal information, and a monthly statement file that shows a cust
> The order-writing department at the Winston Beauchamp Company is managed by Alan Most. The department keeps two types of computer files: (1) a customer file of authorized credit customers and (2) a product file of items currently sold by the company. Both o
> Amanda M is a regional manufacturer and wholesaler of high-quality chocolate candies. The company’s sales and collection process is as follows. Amanda M makes use of an enterprise-wide information system with electronic data interchange (EDI) capability.
> The data-entry department of the Ron Mitchell Manufacturing Company is responsible for converting all of the company’s shipping and receiving information to computer records. Because accuracy in this conversion is essential, the firm employs a strict veri
> There are many accounting blogs on the Internet. Here are some examples. Education Accounting Coach (www.accountingcoach.com/blog) The Accounting Onion (www.accountingonion.com) Sleep on CPA (http://sleeponcpa.blogspot.com/) Fraud The Forensic Accounting
> The Garcia-Lanoue Company produces industrial goods. The company receives purchase orders from its customers and ships goods accordingly. Assuming that the following conditions apply, develop a document flowchart for this company: a. The company receives
> Develop a document flowchart for the following information flow. The individual stores in the Mark Goodwin convenience chain prepare two copies of a goods requisition form (GRF) when they need to order merchandise from the central warehouse. After these fo
> Draw a document flowchart to depict each of the following situations. a. An individual from the marketing department of a wholesale company prepares five copies of a sales invoice, and each copy is sent to a different department. b. The individual invoices
> To view the flowchart shapes in Microsoft Excel, select the following options from the main menu: Insert\Shapes. There should be many of them (using Excel 2016), including many flowcharting symbols. If you allow your mouse t
> Download a copy of the Association of Certified Fraud Examiners Fraud Prevention Checkup, which is available at: www.acfe .com/uploaded Files/ACFE_ Website/Content/ documents/Fraud_Prev_Checkup_DL.pdf. On a separate piece of paper, list the seven areas an
> What company policies or procedures would you recommend to prevent each of the following activities? a. A clerk in the human relations department creates a fictitious employee in the personnel computer file. When this employee’s payroll check is received f
> The U.S. Department of Justice, Office of the U.S. Attorney press release site (www.justice .gove/usao/pressreleases) is a good source for current cybercrimes and fraud. Find a description of a cybercrime not already discussed in this chapter and prepare
> Comment on each of the following scenarios in light of chapter materials. Hint: Use the references at the end of this chapter to help you. a. A legitimate student calls the computer help desk from her cell phone because she has b. An employee at a buildi
> Assume that you started your own law practice 10 years ago, specializing in estate planning, and you currently employ five attorneys, two legal assistants, one legal secretary, and a bookkeeper/receptionist. The firm has always used a manual accounting sys
> How, assume that you work in the internal audit function at a large hospital that is considering a software package to automate the process of complying with the requirements of the American Recovery and Reinvestment Act of 2009 (commonly referred to as
> The following stated policies pertain to the-commerce website for Small Computers, Inc., a personal and handheld computer manufacturer and seller. Privacy Statement We will only use information collected on this website for legitimate business purposes.
> Describe the differences between general-use software and generalized audit software. How might you use spreadsheet software, database software, and word processing software in conducting an audit of fixed assets?
> Choose an industry described in this chapter and find out what vertical market accounting software is available for that industry. You may use resources such as the Internet, trade associations, interviews with organizations within the industry, or interv
> Save Today is a national discount retail store chain with annual revenues of more than $1 billion. It’s a typical bricks-and-mortar operation with accounting software that records sales transactions in real time and tracks inventories on a perpetual basi
> Figure 8-14 is a system flow chart for P. Miesing and Company’s purchase order preparation. Prepare a narrative to accompany the flow chart describing this purchase order preparation process. Include in you
> Novelty Gadgets is a marketer of inexpensive toys and novelties that it sells to retail stores, specialty stores, and catalog companies. As an accountant working for the company, you have been asked to design a product code for the company. In analyzing
> Listed below are several types of accounting data to be coded. For each data item, recommend a type of code (mnemonic, sequence, block, or group) and support your choice. a. Employee identification number on a computer file b. Product number for a sales ca
> To achieve effective separation of duties within a company’s IT environment, the company’s accounting and information processing subsystems should be separate from the departments that use data and perform operational activities. Discuss some of the ways
> Identify one or more control procedures (either general or application controls, or both) that would guard against each of the following errors or problems. a. A bank deposit transaction was accidentally coded with a withdrawal code. b. The key-entry ope
> The Blatz Furniture Company uses an online data input system for processing its sales invoice data, salesperson data, inventory control, and purchase order data. Representative data for each of these applications are shown in Figure 7-14. Identify speci&
> Disgruntled employees can be a significant source of problems for any company as we indicate in this problem. Andi Boyd is a very accomplished computer programmer, but she had a grudge against the company because she did not get a promotion that she thoug
> Identify one or more control procedures (either general or application controls, or both) that would guard against each of the following errors or problems. a. Leslie Thomas, a secretary at the university, indicated that she had worked 40 hours on her re
> Pucinneli Supermarkets is similar to most other grocery store chains that use the 12-digit UPC code on packages to check out customers. For a variety of reasons, it is important that the computer systems using these codes validate them for accuracy and c
> The management of Wiley Coyote Inc. decided that they needed an outside consultant to help them determine which application controls should be implemented for the company’s accounting data processing. In one of the workshops, the seminar leader, Margaret
> Susan Boyd graduated summa cum laude from State University as an accounting major and is now working for a medium-size company. Susan was very clever and quickly realized that she could set up several dummy companies that would direct the company compute
> You have been retained as a consultant to the Bentley Company, and the primary reason they think they need your expertise is to networked PCs. The company maintains fairly extensive databases regarding its customers. These databases include customer profi
> Ron Mitchell is currently working his first day as a ticket seller and cashier at the First Run Movie Theater. When a customer walks up to the ticket booth, Ron collects the required admission charge and issues the movie patron a ticket. To be admitted in
> Listed are 12 internal control procedures or requirements for the expenditure cycle (purchasing, payroll, accounts payable, and cash disbursements) of a manufacturing enterprise. For each of the following, identify the error or misstatement that would be
> The Ashland Company recently hired you to review its control procedures for the purchase, receipt, storage, and issuance of raw materials. You prepared the following comments, which describe Ashland’s procedures. • Raw materials, which consist mainly of
> Rogers, North, & Housour, LLC, is a large, regional CPA firm. There are 74 employees at their Glen Allen, SC office. The administrative assistant at this office approached Mr. Rogers, one of the partners, to express her concerns about the inventory of misce
> The Goochland Company manufactures various types of clothing products for women. To accumulate the costs of manufacturing these products, the company’s accountants have established a computerized cost accounting system. Every Monday morning, the prior we
> Visit a website such as www.top10erp.org that compares several alternative ERP systems. Select a company with which you are familiar and examine the recommended choices for your company’s industry. How do the packages you’ve selected compare to one anoth
> The Lobs, Love & Lessons Tennis Club is a large, regional chain of full-service tennis clubs that cater to the demographics of the region (about 60% of all adults are single in most locations). The clubs each have an indoor swimming pool, exercise equipm
> B&R, Inc. is one of the world’s largest manufacturers and distributors of consumer products, including house hold cleaning supplies and health and beauty products. Last year, their net sales revenues exceeded $5 billion. B&R has multiple information syst
> Tom O’Neal always wanted to own his own business. When he was in high school, he worked evenings and most weekends at a neighborhood bicycle shop. When Tom went to college at the nearby State University, he still came home in the summers and worked at th
> Define the concept of “scalability.” Explain why it might be a good idea for owners of small businesses—and managers in larger businesses—to understand this concept.
> Visit the software websites of two low-end accounting software package vendors and then two ERP vendors. Analyze the descriptions of the software and then describe the differences you see between the low-end packages and the ERP systems.
> Which accounting software features are likely to be most important for the following businesses? Search the Internet for an example of an accounting information system that you would recommend for each of these owners and include your rationale for that
> IBM’s Watson captivated pop culture when it beat two of Jeopardy’s most successful champions. Using your favorite search engine, find an example of how Watson is being used in a business context to improve business outcomes.
> Using your favorite search engine, search for “Gartner Magic Quadrant for Business Intelligence and Analytics Platforms.” Pick one of the vendors from the “Visionaries” quadrant. Research their data analytics/data visualization product offering. What do
> Deceptive Apartments has a policy that requires new tenants to “like” it on Facebook. Some renters don’t mind, but others object because it was not a requirement when they moved it. Further, some argue, the policy is unreasonable because it creates a fal
> List five examples of personal productivity software. For each example you name, also provide an example of how that particular application can help an accountant perform his or her job better, more easily, or more accurately.
> Assume that you are shopping for a new desktop computer. Log onto the Dell Corporation’s website at www.dell.com and develop your own computer system. Include in your system a monitor, keyboard, mouse, and printer, plus whatever additional hardware and s
> It was Friday afternoon, and Dr. Tammy Pucini had seen her last patient for the day. As she sat in her office, staring at the gloomy afternoon sky, she realized that she was both tired and happy. She thought, for example, about how much she had worried th
> Select a type of computer hardware that interests you and write a one-page report on three possible choices of it. Examples include monitors, USB drives, external hard drives, or computer tablets. Your report should include a table similar to the one sho
> Your state has recently decided to install an RFID system for its toll roads. The current plan is to sell nonrefundable transponders for $20 and allow users to deposit up to $1,000 in their accounts. To assist the IT personnel, the system’s planners want
> Brian Fry Products manufactures a variety of machine tools and parts used primarily in industrial tasks. To control production, the company requires the information listed as follows. Design an efficient record format for Brian Fry Products. a. Order numb
> All of the following are acronyms discussed in this chapter. What words were used to form each one and what does each term mean? a. POS b. CPU c. OCR d. MICR e. ATM f. RAM g. ALU h. MIPS i. OS j. MHz k. Pixel l. RGB m. CD-ROM n. Worm o. Modem p. LAN q. S
> Are the following input equipment, output equipment, CPU components, secondary storage devices, or data communications related? a. CRT screen b. ALU c. CD-ROM d. Keyboard e. Modem f. Dot-matrix printer g. Audio speaker h. POS device i. MICR reader j. La
> In Discussion Question 2-1, you discussed intranets and extranets, and identified the importance of each to accountants. Now, assume that you are a partner in a medium sized, local CPA firm. Your firm has 4 partners,10 staff accountants, 1 research assistan
> Visit the home page of a DTSS. How much does your service charge? Do you think these fees are reasonable? Why or why not?
> A number of accounting journals now post back issues or even publish their entire journals online. Access the Journal of Accountancy website at www.aicpa.org (or another website selected by your instructor). Select an article that pertains to a topic in
> The messages below were encrypted using the technique illustrated in Figure 2-11 (using displacement keys other than 5). Using trial and error, decode them. Hint: This task becomes easy if you use an Excel spreadsheet and V Look Up formulas that referenc
> The Internet uses many acronyms. Within the context of the present chapter, what words were used to form each of the following? a. B2B b. B2C c. C2C d. DNS e. EC f. EDI g. Email h. HTTP i. ICANN j. IDEA k. IDS l. IETF m. IoT n. IP address o. ISP p. SaaS
> Springsteen, Inc. is a large furniture manufacturer located in Asbury Park, New Jersey. It sells to furniture wholesalers across the United States and internationally. Revenues last year exceeded $500 million. Currently, the company has over 100 legacy i
> The business models of the breakthrough Internet companies in Figure 2-6 have often been controversial. For example, homeowners often violate local rules governing the rental of their private dwellings, Tesla’s plans to sell cars throug
> Select three Internet websites whose owners sell goods or services and create a table similar to Figure 2-6. Classify each of your websites as B2B, B2C, or C2C. If you are not sure, feel free to use more than one classification. How does t
> Write a one-page paper on each of the following topics as they relate to XBRL: a. What is the history of XBRL? What professional accounting organization helped in the early stages of this concept? b. What is an XBRL specification, and what is the latest v
> Visit the XBRL home page at www.XBRL.org, and read the section entitled “What is XBRL.” Then, do each of the following: a. Select an article from the “What” list of on the home page and write a one-page summary of your findings. b. Search the Internet for
> At the time this book was written, the US Securities and Exchange Commission still supported Edgar—a depository of corporate accounting filings. Log onto Edgar at www.sec.gov/edgar.shtml, click on “Search for Company Filings.” Finally, find and select two
> Create an HTML document of your own, using the example in Figure 2-1 to guide you. Put the name of this assignment in the tag for the heading. Put your name in bold. Include at least one hyperlink to a favorite Web page using the anchor tag. Finally, in
> In this chapter’s “AIS at Work” feature, we discuss the events and SAR surrounding the case of Bernard Madoff. A financial analyst by the name of Harry Markopolos believed it was legally and mathematically impossible for Madoff to be posting such outrageo
> The website of FinCen—the Financial Center Crimes Enforcement Center Network (a department of the US Treasury)—maintains a website at www.fincen.gov. Under “RESOURCES”, you will find links to information for various types of financial institutions including
> Many companies now provide a wealth of information about themselves on their websites. But how much of this information is useful for investment purposes? To help you answer this question, imagine that you have $10,000, which you must invest in the commo
> The participants of such recreational activities as hang gliding, soaring, hiking, rock collecting, or skydiving often create local “birdsof-a-feather” (affinity) organizations. Two examples are the Chicago sky divers (www. chicagoskydivers.com) or the so
> Linda Stanley is the Vice President for Computing and Information Services at State University (SU), a medium-sized, urban university that has experienced a 3% growth in enrollments every year for more than a decade. The university now has almost 22,000
> Select one new trend in the field of accounting information systems today that is not mentioned in the chapter, but that you feel is important. Write a short report describing your findings. Be sure to provide reasons why you feel that your choice of topic
> Shervonne Thomas is the controller at a large manufacturing company located in Chesterfield, Virginia. The company has several divisions that evaluate their performance using a return on assets (ROA) formula (calculated by dividing net profit by the book v
> Look again at the list of assurance services shown in Figure 1-5. What other assurance services can CPAs offer which would take advantage of their AIS expertise? Figure 1-5: Risk Assessment Provide assurance that an organization's set of business r
> Managerial accounting is impacted by IT in many ways, including enhancing corporate performance measurement. How might a university use a scorecard or dashboard approach to operate more effectively?
> Discuss suspicious activity reporting. For example, should such reporting be a legal requirement, or should it be just an ethical matter? Is the majority of SAR activity illegal, or are these just mostly false alarms?
> XBRL is becoming established as the language to create interactive data that financial managers can use in communication. How do you think the use of interactive data might enhance the value of a company’s financial statements?
> Advances in IT are likely to have a continuing impact on financial accounting. What are some changes that are occurring in the way financial information is gathered, processed, and communicated as a result of increasingly sophisticated information technolo
> Hiring an employee and taking a sales order are important business activities, but are not accounting transactions requiring journal entries. Make a list of some other business activities that would not be captured as journal entries in traditional AISs.
> What are intranets? What are extranets? Why are intranets and extranets important to accountants?
> What are some of the unique challenges that mobile devices pose to an organization? What do you see are the trade-offs associated with mobile devices? What are the pros and cons of BYOD?
> Over the past decade, The Retail Cooperative (TRC) successfully acquired a number of smaller retailers, enabling it to grow significantly. As a result, TRC is now one of the largest retailers in Europe, employing over 230,000 people in 25 countries. The c
> Discuss the different backup site options available to organizations. How does the nature of the business influence which site option is chosen?
> What is backup, and why is it important when operating an accounting system?
> What is backup, and why is it important when operating an accounting system?
> Why are business continuity planning and disaster recovery planning so important? How do they complement each other? Identify several reasons why testing these plans is a good idea.
> What controls must be used to protect data that is transmitted across wireless networks?

